In this article, we have covered all the necessary details about Checkm8 jailbreak exploit, & step by step guide to successfully jailbreak iPhone X/8/7 to 4S in 2025 updates.
How to install checkra1n Jailbreak
- checkra1n will be macOS-only at the start, with Linux and Windows versions of the tool being released later down the road
- The macOS release could be CLI-only (this means you’d have to use a command-line interface like Terminal), with a GUI interface launching shortly.
checkra1n jailbreak iOS 13.5
checkra1n 0.10.2 beta add supprot to jailbreak ioS 13.5.
checkra1n 0.10.1 beta released
checkra1n 0.9-beta released ** (old)
Checkra1n Jailbreak Alternatives
You can easily install the app by clicking on the link and it will help you to install popular Jailbreak apps, repos, tweaks, games and more…
CheckRa1n jailbreak Installation Guide –
With Computer/PC
Now you can easily download, CheckRa1n jailbreak Tool through using the above button.
Step 1:
Download the CheckRa1n Jailbreak for iOS 13 – iOS 13.1 – iOS 13.2 Tool onto your computer.
Step 2:
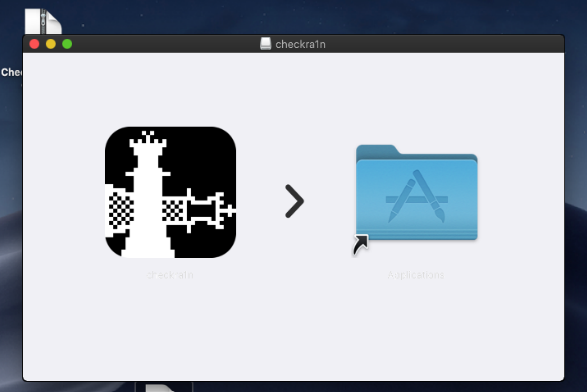
Open dmg file and click checkra1n button
Step 3:
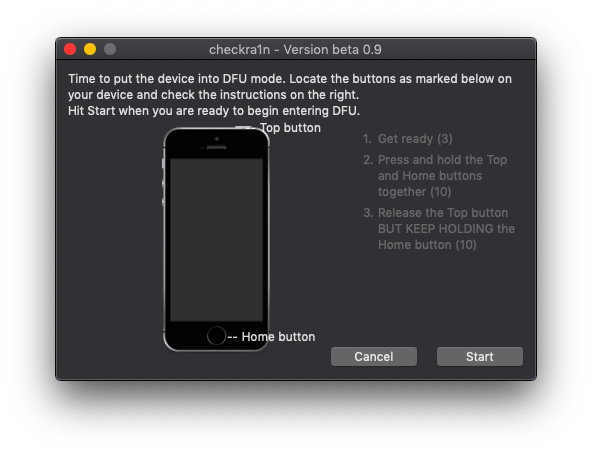
Connect your device to your computer using a USB cable And enter DFU Mode.
(DFU Mode – Press and hold the Power button and Home button together (10 S)
Release the Power button BUT KEEP HOLDING THE Home button)
Step 4:
Press Start Button
Step 5:
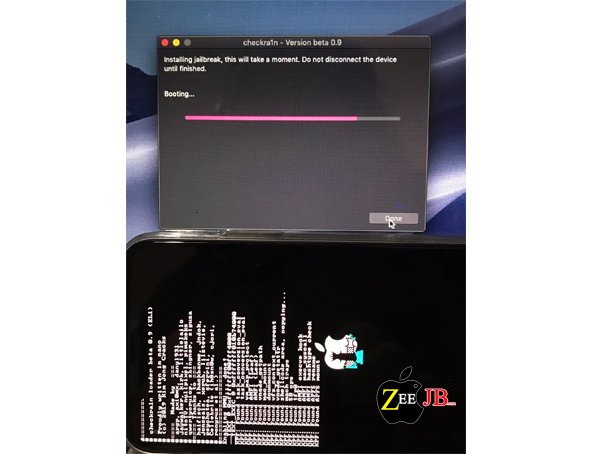
Wait for a few seconds…
Step 6:
After the app is installed, go to Settings -> General -> Profiles (or “Device Management” / “Profiles & Device Management”). Find the profile with your Apple ID and open it.

Open CheckRa1n app on your home screen and hit install Cydia
Tap on the Trust button.
Step 7:
Enjoy it.
Advantages of Checkra1n Jailbreak
- Cannot be patched by any iOS update
- Once jailbroken it will last until user unjailbreak it
- Tap on unc0ver Jailbreak
- Can use for any iOS version (stated by developers)
- Latest coming versions also will be compatible with the jailbreak
- Will be a tethered jailbreak
Does Checkm8 help you?
- Checkm8 is lifetime jailbreak, and Apple does not patch it from iOS upgrade. Only the apple can patch this exploit from Hardware upgrade.
- Without SHSH support it is possible to Upgrade or Downgrade all iOS version
- Checkm8 supported Device can be boot to Android like Dual-booting.
- Upcoming iOS versions are jailbreakable. So you no need to stay any permanent iOS version. Downgrade or upgrade to any jailbreakable iOS version as you wish.
- If you are A5 to A11 Device holder, it does not matter. Still, you are in comfort zone for Checkm8
Can you use Checkm8 for iCloud Bypass?
Upcoming Checkm8 jailbreak exploit allows creating a CFW file. So it could use for bypass iCloud Activation lock.
Checkra1n jailbreak for Checkm8 Exploit
According to Checkm8 tool Developer axi0mx’s Checkra1n is the upcoming tool for Checkm8 exploit.
Update
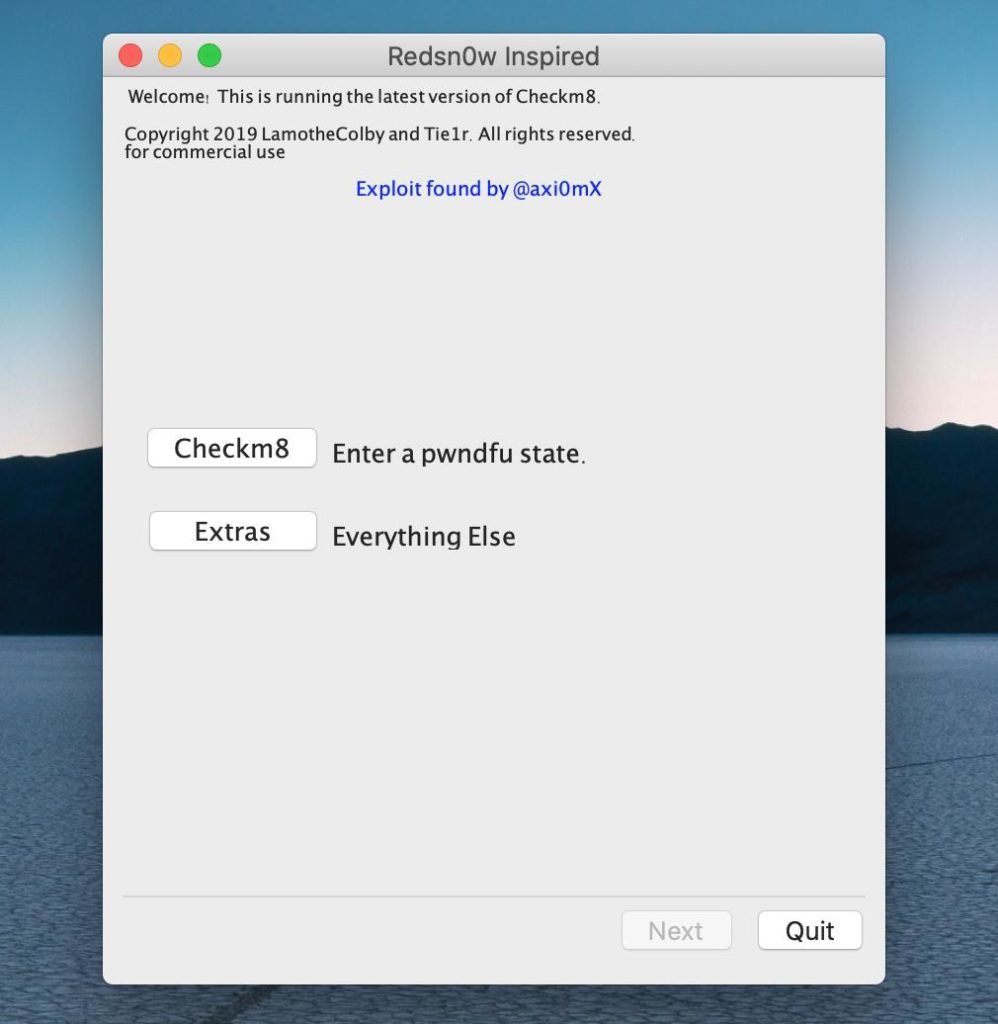
Redsn0w-inspired GUI for checkm8 released on https://github.com/TRCL-lamothecolby/Redsn0w-inspired… (dev – @LamotheColby). It currently supports –
- Verbose boot for iPhone X on iOS 13.1.1 and 13.1.2
- Demote
- Dumping SecureRom
- Entering pwndfu mode
Checkm8 Jailbreak exploit
On the 27th of September hacker, @axi0mX released his checkm8 SecureROM (BootROM) exploit that impacts all iOS devices running on A5 to A11 chipsets.
checkm8 jailbreak exploit supports with all Apple products released between 2011 and 2017, & spanning eight generations of devices, from iPhone 4S to iPhone 8 and X
When release Checkra1n Jailbreak tool?
Checkra1n jailbreak tool could release soon. So do not upgrade your iOS version above iOS 13. Install iOS update blocker to stop OTA updates.
What is Checkra1n jailbreak?
Checkra1n iOS 13.1.2 jailbreak based on recently released checkm8 bootrom exploit has essentially been announced.
Luca Todesco and now axi0mX has taken to Twitter to share a screenshot of an Apple iPhone being exploited by a custom-built jailbreak that he is calling checkra1n (like Geohot’s limera1n).
And yes, this jailbreak is built on top of the checkm8 exploit, which means that it will offer compatibility for all A5-A11 devices regardless of the firmware that they are running.
Is checkm8 a Jailbreak?
Checkm8 is an exploit and not a jailbreak. It is, in fact, possible to leverage Checkm8 to load custom or modified kernels and support additional jailbreak capabilities or sideloaded apps, but so far this has not been publicly achieved.
Since the exploit itself doesn’t persist across device reboots, persistence and other critical modifications would require additional vulnerabilities in iOS or its kernel.
iOS Compatibility
All the iOS versions (which is run on above-supported devices including latest iOS 13.2, iOS 13.1.2, iOS 13.1.1, iOS 13.1, iOS 13)
Compatible devices – Checkm8 jailbreak
- iPhone 4S,
- iPhone 5, 5C & 5S,
- iPhone 6 / 6 Plus, 6S / 6S Plus,
- iPhone 7 / 7 Plus,
- iPhone 8 / 8 Plus and iPhone X,
- As well as all iPods from iPod Touch 5 to iPod Touch 7th Generation, and all iPads that are not A12.
Benefits and constraints
That the jailbreak uses a new exploit named Checkm8 that exploits vulnerabilities in Apple’s Bootrom (secure boot ROM) to grant phone owners full control over their device.
Unlike just about every jailbreak exploit released in the past nine years, it targets the iOS bootrom, which contains the very first code that’s executed when an iDevice is turned on. Because the bootrom is contained in read-only memory inside a chip, jailbreak vulnerabilities that reside there can’t be patched.
That benefit is countered by the threat that the same jailbreak will give hackers a new way to install malware or unlock iPhones that are lost, stolen, or confiscated by unscrupulous authorities.
Checkm8 Jailbreak Features
Features the Checkm8 exploit allows include as mentioned below:
- Jailbreak and downgrade iPhone 3GS (new bootrom) with alloc8 untethered bootrom exploit.
- Pwned DFU Mode with steaks4uce exploits for S5L8720 devices.
- Pwned DFU Mode with limera1n exploits for S5L8920/S5L8922 devices.
- Pwned DFU Mode with SHAtter exploits for S5L8930 devices.
- Dump SecureROM on S5L8920/S5L8922/S5L8930 devices.
- Dump NOR on S5L8920 devices.
- Flash NOR on S5L8920 devices.
- Encrypt or decrypt hex data on a connected device in pwned DFU Mode using its GID or UID key.
How to install Checkm8 Jailbreak
Install checkm8 jailbreak exploit with the computer ( Just works only Mac or on Linux. No Windows tool for now. )
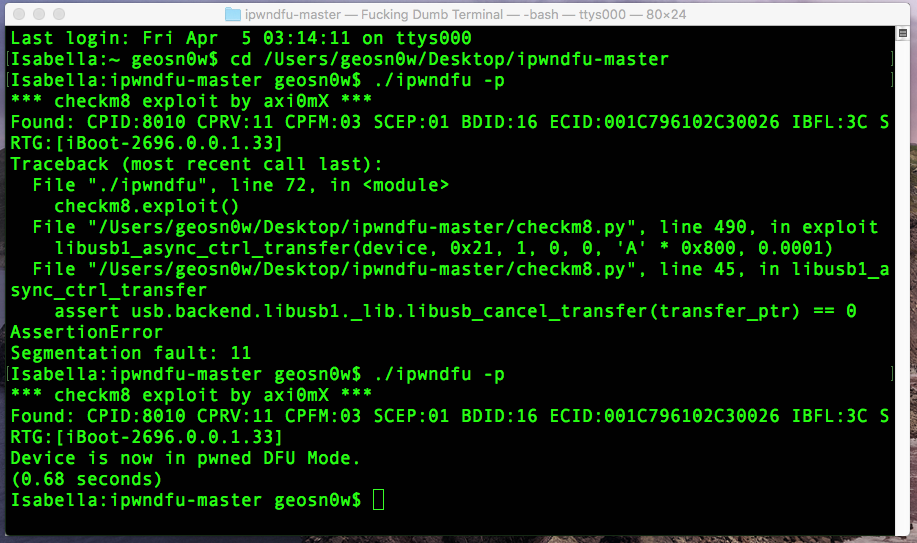
- Download iPwnDFU from here: https://github.com/axi0mX/ipwndfu
- Unpack the ZIP file on your Desktop.
- Open Terminal and run “cd /PathToYourExtractedFile” (change PathToYourExtractedFile to the actual path).
- Connect your iDevice to the computer using a USB cable.
- Put the device in DFU Mode. Before iPhone 7, you do it by pressing and holding Power + Home until the screen is off, wait a few seconds, release the POWER button but keep pressing the HOME button for another 10 seconds. the screen should remain black. For iPhone 7 and newer, you need to press and hold POWER + VOLUME DOWN until the screen is off, wait a few seconds, release the POWER button and keep pressing the VOLUME DOWN button for another
- In the Terminal run “./ipwndfu -p”. If you get an error, run it again until you get a message telling you the iDevice is now in Pwned DFU mode.
- The Pwned DFU mode will remain until the phone reboots. You should not see anything on the screen (black screen). This basically it. You can now DUMP the ScureROM, demote the device to enable JTAG, and soon you’ll be able to restore CFWs, do downgrades, etc.

CODE AVAILABLE ON GITHUB
Axi0mX’s jailbreak is available on GitHub. The code is marked as a “beta” release.
Most jailbreaking exploits are usually packaged in easy to use tools. For the moment, Checkm8 is in a very raw form and it isn’t recommended for users without proper technical skills as it could easily result in bricked devices.Axi0mX also published a Jailbreak guide, Others features will be added soon, he said.
“A bootrom exploit for older devices makes iOS better for everyone. Jailbreakers and tweak developers will be able to jailbreak their phones on the latest version, and they will not need to stay on older iOS versions waiting for a jailbreak. They will be safer.
”Axi0mX said this vulnerability cannot be exploited remotely, the attackers need to have physical access to the device.
Quick start guide for checkm8
- Use a cable to connect the device to your Mac. Hold buttons as needed to enter DFU Mode.
- First, run
./ipwndfu -pto exploit the device. Repeat the process if it fails, it is not reliable. - Run
./ipwndfu --dump-romto get a dump of SecureROM. - Run
./ipwndfu --decrypt-gid KEYBAGto decrypt a key bag. - Run
./ipwndfu --demoteto demote the device and enable JTAG.
iOS 11 to iOS 13.5 Jailbreak solutions
In this section, I am going to show you how to install jailbreak tweaks without fully jailbreak your iDevice
iOS 13 – iOS 13.1.1 and iOS 13.1.2 Jailbreak solution
There are five jailbreak solutions for the iOS 13 jailbreak. Also, you can use these jailbreak solutions for iOS 12, iOS 13, iOS 13.2 and other iOS beta profiles.
PikZo jailbreak
PiKzo is the most popular alternative jailbreak solution for checkm8 jailbreak exploit, also it is jailbreak repo extractor.
By using PiKzo jailbreak you can easily install new jailbreak repos, tweaks, icon themes, hacked games, nulled apps, and many more features.
PiKzo jailbreak is now available.
Features
+ Install Awesome Jailbreak apps
+ Collection of Themes
+ App store banned apps/games
+ Premium ++ Apps
+ Game Emulators
+ World’s 1st web-based iPhone OS
+ Run old Mac, Windows or Ubuntu
+ Hacked App store apps & games & many more
The new UO4S App Store (u04) provides the ability to install unc0ver Jailbreak applications without a computer. (revoke fixed for uncover jailbreak )
UOS store is one of the best jailbreak solutions for iOS 13, iOS 13.1, iOS 13.2, iOS 13.2.3, iOS 13.3 and It has 1000+ Jailbreak Tweaks, Cydia-apps, Hacked Games and more…
Bregxi Jailbreak
Bregxi offers hundreds of jailbreak apps and tweaks including Cydia and Sileo demo versions to jailbreak iOS 12.3 – 12.4
Bregxi is another Jailbreak repo extractor for iOS 13. Bregxi iOS 13 compatibility added together iOS 13 final release. The 1st time Bregxi released for iOS 12.3 Jailbreak.
Checkra1n Jailbreak iOS 13.4
checkra1n Beta 0.10.0 Available
Chekra1n team has released a new beta of their tool (v0.10.1) with a bunch of bug fixes and support for iOS 13.4 and iOS 13.4.1.
More about Checkra1n Jailbreak iOS 13.4 >>>
You may also like:
| iOS 17.1 jailbreak | iOS 17.2 jailbreak |
| iOS 17.3 jailbreak | iOS 17.4 jailbreak |
| iOS 17 github | Udid masters certificates |